 |
| SANS Cisco Mind Map |
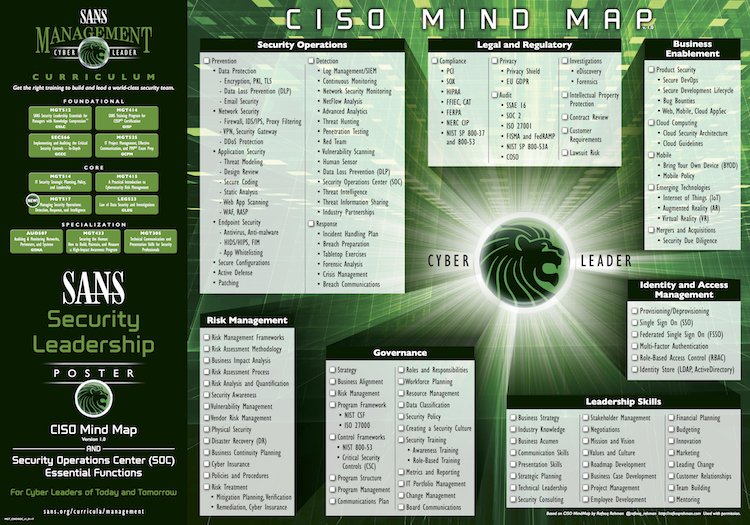
A CISO (Chief Information Security Officer) has a complex role within a company. They have a wide array of tasks to perform, that involves many differing parts, which the average individual is not always aware of.
CISO Mind Map is an overview of responsibilities and ever expanding role of the CISO. This Security Leadership poster made by SANS shows exactly the matters a CISO needs to mind when creating a world class IT Security team. It also highlights the essential features necessary of a Security Operations Centre (SOC).
To make this chart more practical, I put them into the tables and will update it with some technologies and thoughts applied in my daily work. This update will last a long term. It will be put into navigation bar for easy access.
Security Operations
|
Prevention
|
Detection
|
Response
|
|
|
|
Legal and Regulatory
| Compliance | Privacy | Audit | Investigation |
|
|
|
|
| Intellectual Property | Contract Review | Customer Requirments | Lawsuit Risk & Acts |
|
|
|
|
| Risk Framework | Risk Assessment Methodology | Business Impact Analysis |
|
|
|
| Risk Assessment Process | Risk Analysis and Quantification | Security Awareness |
|
|
|
|
| Vulnerability Management | Vendor Risk Management | Physical Security |
|
|
|
| Disaster Recovery (DR) | Business Continuity Planning | Risk Treatment |
|
|
|
|
| Policies and Procedures | ||
|
||
| Product Security | Cloud Computing | Mobile |
|
|
|
| Emerging Technologies | Mergers and Acquisitions | |
|
|
Governance
| Strategy | Business Alignment | Risk Management |
|
|
|
| Program Frameworks | Control Frameworks | Program Structure |
|
|
|
| Program Management | Communications Plan | Roles and Responsibilities |
|
|
|
|
| Workforce Planning | Resource Managemnet | Data Classification |
|
|
|
|
| Security Policy | Create a Security Culture | Security Training |
|
|
|
| Metrics and Reporting | IT Portfolio Management | Change Management |
|
|
|
| Board Communications | ||
|
|
|
Identify and Access Management
|
Provisioning/
Deprovisioning
|
Single Sign On
(SSO)
|
Federated Single Sing on (FSSO)
|
|
|
|
|
|
Multi-Factor Authentication
|
Role-Based Access Control (RBAC)
|
Identity Store (LDAP, ActiveDirectory) |
|
|
|
|
Leadership Skills
| Business Strategy | Industry Knowledge | Business Acumen |
|
|
|
|
| Communication Skills | Presentation Skills | Strategic Planning |
|
|
|
|
| Technical Leadership | Security Consulting | Stakeholder Management |
|
|
|
| Negotiations | Mission and Vision | Values and Culture |
|
|
|
|
| Roadmap Development | Business Case Development | Project Management |
|
|
|
| Employee Development | Financial Planning | Budgeting |
|
|
|
|
| Innovation | Marketing | Leading Change |
|
|
|
|
| Customer Relationships | Team Building | Mentoring |
|
|
|
|
Note: ISO = Information Security Office
Another CISO Mind Map example:
Note: The original image concept was created by Rafeeq Rehman and later redesigned by Momentum Partners.
